TECHNOLOGY
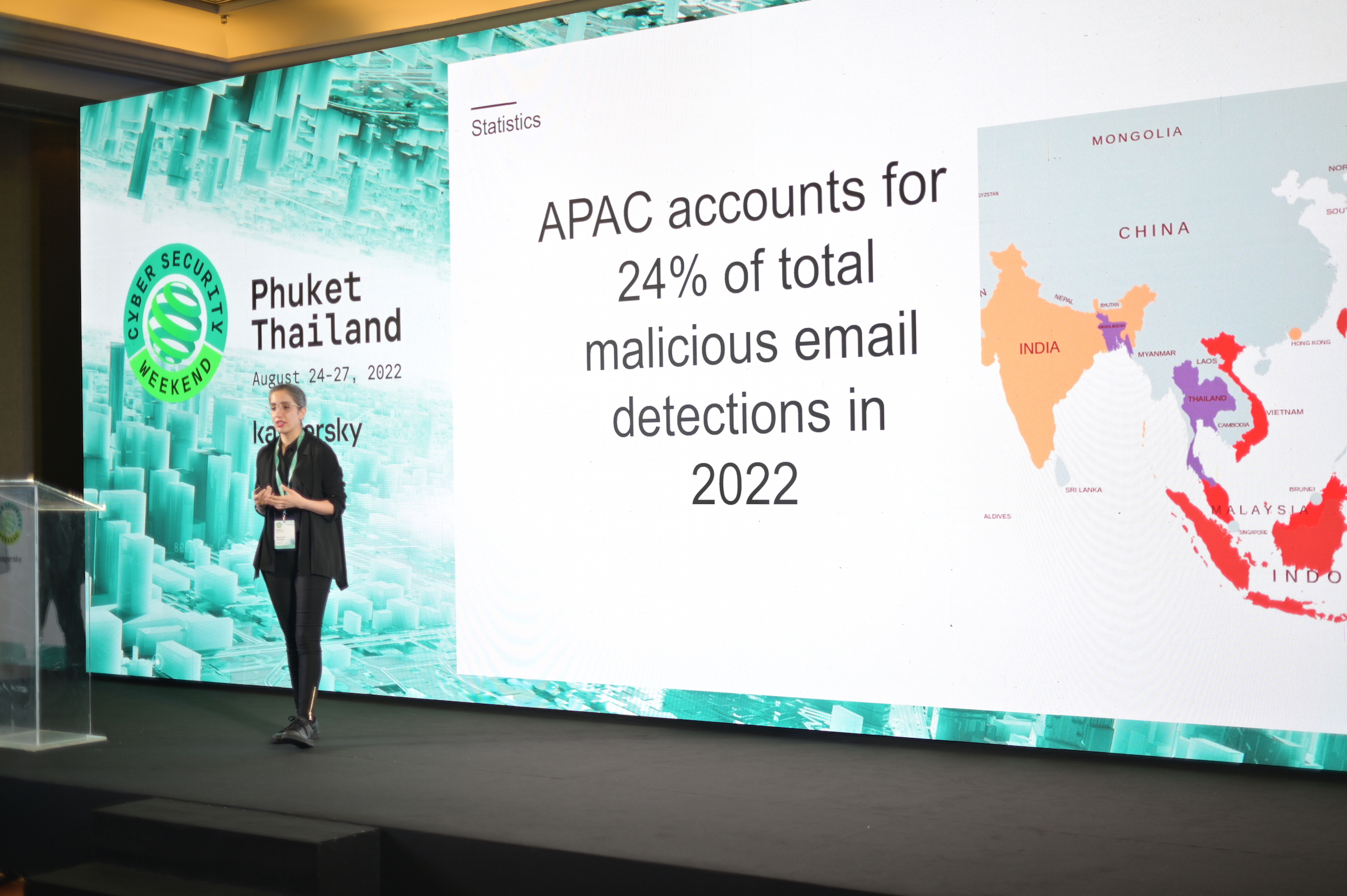
You’ve Got Spam Mail: APAC accounts for a quarter of global malicious emails in 2022
September 7, 2022 2:05 p.m.
Spam mails have evolved since the first one was sent back in 1978. Its evolutions span from the techniques, tactics, and the latest trends cybercriminals piggyback on to make it more legitimate-looking and urgent-sounding – an effective formula to prey upon an unsuspecting user.
One of Kaspersky’s elite researchers, Noushin Shabab, probed into the spam threat landscape in Asia Pacific (APAC) this year to answer – what if emails do not get opened?
Shabab, presented in front of selected media from the region during Kaspersky’s 8th APAC Cyber Security Weekend, revealed that the region received 24% of the global malicious spam mails being detected and blocked by Kaspersky solutions. This means one in four junk electronic messages were delivered to computers in APAC.
Noushin Shabab, Senior Security Researcher for Global Research and Analysis Team (GReAT) at Kaspersky
Malicious spam is not a technologically complex attack, but when done with sophisticated social engineering techniques, it poses a severe threat to individuals and enterprises alike. These junk mails are sent out in mass quantities by spammers and cybercriminals who are looking to do one or more of the following:
- Make money from the small percentage of recipients that actually respond to the message
- Run phishing scams – in order to obtain passwords, credit card numbers, bank account details, and more
- Spread malicious code onto recipients’ computers
In 2022, more than half (61.1%) of the malicious spam detected in the region targeted Kaspersky users from Vietnam, Malaysia, Japan, Indonesia, and Taiwan.
Shabab cited three main factors which cause the bulk of spam emails targeting APAC —- its population, the high adoption of e-services, and the pandemic lockdowns.
The APAC region has almost 60% of the world’s population and this means that there are more potential victims for scammers here compared to other parts of the world. The extensive use of online services such as online shopping and other online platforms for day-to-day activities here also makes individuals more susceptible to falling victim to scams. There is also the lingering pandemic aftermath which led to lockdowns and work-from-home set up in the region where people took their work computers home. Home networks are usually less protected from cyberattacks.
“Since 2018, the number of malicious spam mails detected by our solutions has seen a gradual decline after its peak in 2019. This, however, does not equate to our mailboxes being cleaner and safer. Our constant monitoring of the current and new Advanced Persistent Threats (APTs) operating in Asia Pacific showed that majority of these notorious threat actors use targeted phishing called spear phishing to crack into an organization’s systems,” reveals Noushin Shabab, Senior Security Researcher for Global Research and Analysis Team (GReAT) at Kaspersky.
The most recent example of an APT targeting key entities in APAC through sophisticated malicious mails is the “Sidewinder” threat actor. Since October 2021, the Sidewinder threat actor has been using new malicious JS code with recently created C2 server domains. The attacker, also known as Rattlesnake or T-APT4, targets victims with spear-phishing emails containing malicious RTF and OOXML files.
Known for targeting military, defense and law enforcement agencies, foreign affairs, IT, and aviation entities in Central and South Asia, Sidewinder is considered one of the most prolific threat actors monitored in the APAC region. Kaspersky experts also recently found spear phishing documents which appear to be aimed at future targets in Singapore.
Some of the main characteristics of this threat actor that make it stand out among the others are the sheer number, high frequency and persistence of their attacks, and the large collection of encrypted and obfuscated malicious components used in their operations. Kaspersky experts, who have been monitoring Sidewinder since 2012, have detected over a thousand spear phishing attacks by this APT actor since October 2020.
Sidewinder also continues to expand its victimology and to sharpen its phishing tactics.
For instance, to reduce the suspicion raised by some of their spear-phishing documents that had no text content, the group followed their first attempt to attack the victim – a spear-phishing email containing a malicious RTF exploit file – with another similar email, but in this case, the title of the malicious document was “_Apology Letter.docx”, and it contained some text explaining that the previous email was sent in error and that they are reaching out to apologize for that mistake.
“There are many more well-oiled APT groups like Sidewinder who are constantly upgrading their tools and tactics to target high-profile victims in APAC through believable spam and phishing emails. The implication for enterprises and government organizations here is that a single malicious email when clicked can crumble your most sophisticated defenses, and usually, APTs like Sidewinder just need one door to open, one machine to infect, and then it can hide and stay undetected for long,” Shabab adds.
APTs target any sensitive data; one doesn’t need to be a government agency, major financial institution, or energy company to become a victim.
The major danger of APT attacks is that even when they are discovered and the immediate threat appears to be gone, the hackers may have left multiple backdoors open that allow them to return when they choose. This increases the importance of guarding mailboxes – an entry point they usually exploit to get a foothold of an organization’s networks.
Employees across all ranks need to be aware of the threats, such as the possibility of bogus emails landing in their inboxes. Besides education, technology that focuses on email security is necessary.
To be able to search for potential spear-phishing signs without diminishing the company’s actual security, Kaspersky suggests private and public companies to install protective anti phishing solutions on mail servers as well as on employee workstations.
Enterprises should also utilize advanced security software that can detect sophisticated APT attacks.
For governments, Shabab suggests defining better spam regulations to curb spam risks. “Fewer spam emails from legitimate organizations means people are less used to receiving unexpected emails every day and are more vigilant when they are being targeted with malicious spear phishing emails,” she adds.
TECHNOLOGY
All-new MacBook Neo launches at Power Mac Center

9:22 p.m. April 24, 2026
Premier Apple partner Power Mac Center (PMC) unveiled the all-new MacBook Neo in a fun and vibrant simultaneous launch in Greenbelt 3 and SM Megamall.
Customers who joined the launch received the event exclusive bundle including an AirPods Pro 2 and AirTag 4-pack, stackable with over P12,000 worth of freebies for those with qualified pre-orders. In addition, those in Greenbelt 3 and SM Megamall who lined up until 7PM also got a chance to win up to P600,000 worth of prizes (P300,000 per location).
While attendees were the first to access exclusive perks, PMC is extending its opening promotions over the coming days, ensuring more customers can take part in the excitement.
“We are taking Apple fans on a lifestyle journey worthy of the anticipation for the new MacBook Neo. With every device Power Mac Center launches, we make sure our customers know we stand behind their purchase, helping them choose better, set up faster, and get more out of what they’re upgrading to,” PMC Director for Marketing and Product Management Joey Alvarez.
Mac&Me: Easy to use and easy to own, Made for More
As the premier Apple partner in the Philippines, PMC extends its expertise to support customers, reinforcing how the Mac is made for more than ordinary, with powerful capabilities in completing tasks both for work and play.
Now available in all Power Mac Center stores nationwide, the MacBook Neo is easy to use and easy to own with these exclusive offers. Terms and conditions apply.
- Accessories: Enjoy up to 50% off on a wide selection of accessories until April 30, 2026. This offer is valid for straight payments only and is available with any MacBook Neo payment option.
- 1 Infinite: As a limited “double burn” offer (1 point = P2) from PMC’s loyalty program 1 Infinite, members can redeem up to 2,500 points (P5,000 off), with no minimum spend required. This offer is applicable to both device and accessory purchases and is valid from April 23 to 26, 2026 only.
- UpTrade: Score up to P4,000 in additional trade-in value when you trade in your MacBook Air (M2 or earlier) and upgrade to the all-new MacBook Neo or MacBook Air (M5) from April 23 to May 10, 2026. Offer available at all Power Mac Center stores nationwide.
- Mobile Care and Basecamp: Customers who purchase the MacBook Neo until April 30, 2026 can also receive a 90-day complementary software fix from Mobile Care Service Center, PMC’s official service arm, and free training for MacBook Neo + AI Toolkit for Beginners provided by Basecamp, PMC’s official training arm.
- To avail the free training, please register here <https://docs.google.com/forms/d/e/1FAIpQLSe_z0LeHOubTSrH4guDE7H1gaZICevgaQ15fF0tqxI7CB-aQw/viewform>.
- Partners: Get special Grab vouchers on purchases of the MacBook Neo until April 24, 2026.
- Education, SMB, and Enterprise: PMC also offers special Education pricing for students and members of the academe. Meanwhile, businesses and organizations looking to boost their operational efficiency and service delivery can approach any PMC store for a consultation on Apple integration.
Get the best deals with your cards and credit providers
Major bank and non-bank financial institutions offer flexible payment options of up to 36 months installment, 0% interest, Buy Now Pay Later modes, cashbacks, and bonus Power Mac Center Gift Certificates. Do note that these offers are available via in-store purchases only. Check with your financial providers for the full mechanics.
Before completing your purchase, make sure you’re a member of 1 Infinite. To join, download the 1 Infinite app in the App Store <http://bit.ly/4hljdr2> or Google Play <https://bit.ly/42ovsyK> and create an account or log in using your registered email address.
Present your membership when transacting in stores or input details in the Web Store <powermaccenter.com> to earn points, redeem rewards, and enjoy perks from Basecamp and Mobile Care. For full details, visit the site <https://powermaccenter.com/pages/1-infinite>.
Live launch with musical sets and interactive games
The MacBook Neo introduction unfolded as a full launch experience, with performances and interactive activities energizing the crowd before the official unveiling. Headlined by DJs Vernard Tan (in Greenbelt 3) and Ailishia (in Megamall), the shows set the tone for the night designed to engage this generation of tech consumers.
The event was supported by Power Mac Center’s brand partners Belkin, STM, BPI, UnionBank, and Home Credit, as well as Shokz, in partnership with 1 Infinite.
Don’t miss exciting announcements and special promos! Follow the OFFICIAL Power Mac Center accounts on Facebook, Instagram, X, TikTok, Viber, and YouTube.
#PMCExperience #MacMadeForMore
TECHNOLOGY
Xiaomi Fan Festival 2026 brings April deals across phones, pads, and smart devices

9:30 p.m. April 12, 2026
April is one of the better times this year to look at a Xiaomi upgrade. Xiaomi Fan Festival, the brand’s annual celebration for its fans; is now live in the Philippines under the theme “Smart Living, Made Yours,” running through April 30 at Xiaomi Authorized Stores, participating multi-brand retailers, and Xiaomi community channels.
The campaign spans the full lineup: phones from flagship to entry-level, tablets, wearables, TVs, and more. Most buyers will find at least one clear entry point.
Smartphones
At the top of the range is the Xiaomi 17, priced at ₱55,999 with a free Xiaomi Smart Band 9 Pro. For buyers who want a strong performer without going all the way to the flagship tier, the Xiaomi 15T Pro is available at ₱39,999 with a free Xiaomi Backpack, and the Xiaomi 15T comes in at ₱26,999 down from ₱28,999, with a free Xiaomi Neck Pillow.
The REDMI Note 15 Series covers the mid-range with four variants and a consistent Home Credit angle: shoppers can get an exclusive ₱500 discount per unit on any REDMI Note 15 Series device via Home Credit 0% interest installment plan, and a free month on Viu Premium. The REDMI Note 15 Pro+ 5G is priced at ₱27,999 with a free Xiaomi umbrella, the REDMI Note 15 Pro 5G starts at ₱19,999 with the same freebie, and the REDMI Note 15 5G runs from ₱14,999. At the most accessible end, the REDMI 15 starts at ₱8,999; a practical everyday pick for students and first-time buyers.
Pads
The Xiaomi Pad 8 Pro at ₱38,999 and the Xiaomi Pad 8 at ₱29,999 each come with the keyboard already in the box, plus a free Xiaomi Smart Band 9 Active, boasting a more complete setup from day one, whether the use case is work, school, or content. Both are also available via Home Credit 0% interest installment.
Below those, the REDMI Pad 2 lineup offers three tiers: the REDMI Pad 2 Pro 5G from ₱19,999, the REDMI Pad 2 Pro from ₱15,999, and the REDMI Pad 2 from ₱10,999 which gives students and households a range of screen sizes and specs without stepping into premium territory.
Wearables, TVs, and more
The wearables selection runs wider than the headline picks. The Xiaomi Smart Band 10 is available in Standard (₱2,699) and Ceramic Edition (₱3,799), with the Xiaomi Smart Band 10 Pro at ₱3,899 for buyers who want more. On the more accessible end, the Xiaomi Smart Band 9 Active is ₱1,399, and the REDMI Watch 5 Active comes in at ₱1,899. The REDMI Watch 5 is priced at ₱2,899.
For the living room, the Xiaomi TV A Series starts at ₱8,990 for the 32-inch and ₱12,990 for the 43-inch. Also in the lineup: the REDMI Buds 8 Lite at ₱1,299 and the Xiaomi Power Bank 10000mAh at ₱1,099.
Payment options
The Home Credit ₱500 discount is applicable to the REDMI Note 15 series while all smartphones and pads will come with 0% interest installment and Viu Premium 1-month voucher offer. That offer runs from April 1 to June 30, 2026; well past the main XFF window, giving you more time to sort out a payment plan before committing.
The deals listed here cover the main highlighted offers, but the full XFF 2026 lineup is broader. For complete mechanics, freebie eligibility per variant, and model availability, visit your nearest Xiaomi Authorized Store or participating retailer. For the Home Credit discount and installment options, ask at any participating Home Credit hub.
TECHNOLOGY
Quick Flicks and Pro Clicks: Logitech brings fastest click technology with Latest PRO X2 SUPERSTRIKE

1:11 p.m. March 26, 2026
Logitech G raises the bar for competitive gaming performance once again with the launch of the PRO X2 SUPERSTRIKE, a next-gen wireless mouse that combines inductive analog sensing with real-time haptics.
Designed for elite precision and total control, the PRO X2 dramatically reduces click latency, enhances responsiveness, and gives players the power to personalize their click intensity like never before.
Industry-Leading Click Technology
Featuring a patent-pending SUPERSTRIKE technology, an industry-first innovation, the PRO X2 transforms how every mouse click is activated and felt. This new technology allows players to reduce the required travel distance to send the click signal. Improvements in click delay are shown to reach up to 30 milliseconds based on internal testing. This drastically transforms the way players compete and provides them the decisive edge they need to win virtual battlefields.
The PRO X2 introduces the Haptic Inductive Trigger System (HITS), which replaces traditional microswitches found in gaming mice. This system drastically improves click latency performance by sending tactile feedback to players so each click is felt the moment the signal reaches the PC.
By combining trigger response optimization with real-time click haptics, Logitech G sets a new benchmark in competitive mouse performance through the PRO X2.
Customizable Esports-Level Gaming Performance
Developed in collaboration with elite esports teams G2 Esports, NAVi, and BLG, the PRO X2 is made to meet the demands of high-level competitive play. Every element of the mouse is designed to support players in fast decision-making, precise execution, and unmatched consistency, whether competing in a professional environment or grinding ranked matches at home.
Beyond its impressive click system, the PRO X2 also introduces 10 selectable actuation steps, allowing players to fine-tune the actuation point of both main buttons. This level of control enables them to calibrate every click depth to match their preferred playstyle, role, or specific game requirements with zero hassle. These adjustments can be made seamlessly through Logitech G HUB software, giving them the flexibility to edit their settings without disrupting their momentum.
The PRO X2 also features LIGHTSPEED wireless technology that blends comfort and efficiency by delivering up to an 8 kHz report rate of untethered freedom. This end-to-end wireless solution ensures that every click and movement registers with exceptional speed and stability, earning the trust of esports professionals worldwide.
Precision Tracking Without Setbacks
Harnessing Logitech’s elite HERO 2 sensor, the PRO X2 SUPERSTRIKE enables a reliable 888 IPS tracking speed with sub-micron precision, up to 44,000 DPI mouse sensitivity, and over 88G acceleration. For players, this level of control not only supports quick wrist flicks and controlled micro-adjustments but also helps in split-second decisions that require fast reaction. Movements are assured to have zero smoothing, acceleration, or filtering, giving players the chance to showcase their raw and unfiltered skills.
Lightweight Design Built for Long Competitive Sessions
Following the award-winning design of the SUPERLIGHT 2, the PRO X2 weighs 61 grams to support fluid movements and long competitive sessions. Additionally, it comes with a long-lasting battery, reaching up
90 hours of constant use, to allow players to focus on their games without worrying about charge times.
The PRO X2 SUPERSTRIKE sets a new benchmark in player-controlled click innovation that redefines what competitive gaming hardware can deliver. Through Logitech’s advancing technologies, it brings together ultra-responsiveness and absolute control for a reliable wireless virtual performance.
Logitech G’s latest gaming mouse is priced at PHP 11,945 and is available exclusively on Shopee and Logitech Authorized Retail Partners and Gaming Specialists. To learn more about the product and upcoming product releases, follow Logitech G on Facebook. You may also visit http://www.logitechg.com for more product offerings.

















